Navigating the landscape of modern cybersecurity can sometimes feel like walking a tightrope. On one hand, you want the most robust protection possible to shield your data from evolving threats; on the other, you need your computer to actually function without your antivirus software snatching away legitimate files. If you have ever wondered how to exclude files from windows security, you are certainly not alone. This guide provides a deep dive into the mechanics of Windows Defender, the nuances of safe exclusions, and how to recover data if your security settings have been a bit too aggressive.
What Is Windows Security and Why It Scans Files
Windows Security, formerly known as Microsoft Defender Antivirus, serves as the primary line of defense for hundreds of millions of users worldwide. It is a comprehensive, built-in security suite designed to provide real-time protection against viruses, malware, and ransomware. Because it is integrated directly into the Windows kernel, it has a “birds-eye view” of every operation your CPU performs.
The fundamental reason it scans files is to verify their digital “signature” and behavioral patterns. Every time you download a document, plug in a USB drive, or run a new application, Windows Security cross-references the file’s data against a massive cloud-based database of known threats. This process is essential because, in 2026, polymorphic malware can change its code to avoid detection, making constant vigilance a necessity.
How Real-Time Protection Works
Real-time protection is the “always-on” component of Windows Security. It operates using an interceptor model. When an application attempts to access a file, the operating system pauses the request for a millisecond. During this tiny window, the antivirus engine inspects the file. If the file is deemed safe, the request proceeds. If it matches a known malware definition or exhibits “heuristic” (suspicious) behavior, the antivirus terminates the process and often “quarantines” or deletes the file to prevent system-wide infection.
Common Reasons Files Get Flagged
While the system is highly accurate, it isn’t perfect. Several factors can lead to a file being flagged:
- Unsigned Code: Developers who haven’t paid for a digital certificate may find their apps flagged.
- Heuristic Overreach: If a program performs actions similar to malware (like modifying system registry keys), it might trigger an alert.
- Obfuscated Scripts: Highly compressed or encrypted files often look suspicious to scanners because they cannot “see” inside them easily.
Why You Might Need to Exclude Files
Understanding how to exclude files from windows security is a vital skill for power users, developers, and gamers. There are instances where the software is simply too protective, hindering productivity or preventing specialized tools from running.
False Positives Explained
A false positive occurs when the antivirus identifies a harmless file as a threat. This is common with specialized data recovery tools, niche engineering software, or custom scripts used in IT environments. If you are 100% certain that a file is safe—perhaps you wrote the code yourself—excluding it is the only way to keep Windows from repeatedly blocking or deleting it.
Performance Optimization Cases
Antivirus scanning consumes CPU cycles and Disk I/O. For tasks that involve heavy file reading and writing—such as compiling software code, rendering 4K video, or running large databases—the constant interference of Windows Security can cause a 10% to 15% drop in performance. By excluding the specific project folders, you allow your hardware to run at its full potential without the “overhead” of constant inspection.
Important Safety Considerations Before Excluding Files
Before we jump into the technical steps, we must address the risks. Creating an exclusion is essentially creating a “blind spot” in your security.
Risks of Adding Exclusions
The primary risk is that if a virus manages to land inside an excluded folder, Windows Security will ignore it. Malware authors often target common exclusion paths (like temporary folders or specific app directories) to hide their malicious payloads. Therefore, you must be absolutely certain of the source of the file you are excluding.
Best Practices for Safe Exclusions
To maintain a secure environment, follow these professional tips:
- Be Granular: Never exclude a whole drive (like C:). Instead, exclude a specific file or a single sub-folder.
- Verify Sources: Use tools like VirusTotal to scan a file with multiple antivirus engines before adding it to your Windows Security exclusion list.
- Temporary Exclusions: If you only need a file for a quick task, remember to remove the exclusion once the work is finished.
Types of Exclusions in Windows Security
Windows offers four distinct ways to whitelist items. Choosing the right one is key to maintaining the balance between usability and safety.
File Exclusions
This targets a specific file by its exact path (e.g., C:\Tools\my_app.exe). This is the most recommended method because it limits the “hole” in your security to a single point.
Folder Exclusions
This tells the system to ignore everything inside a specific directory. While convenient for developers with large project libraries, it is inherently riskier.
Process Exclusions
Instead of a file on the disk, this excludes a program currently running in the memory. This is helpful if a legitimate background service is being throttled by the antivirus.
File Type Exclusions
You can exclude all files with a specific extension, such as .log or .db. This should be used with extreme caution, as malware can easily masquerade as a common file type.
Step-by-Step Guide to Exclude Files (Windows 11 & 10)
If you are ready to proceed, follow these steps precisely to ensure the exclusion is applied correctly.
Step 1 – Open Windows Security
Click on the Start button and type Windows Security. Alternatively, look for the small shield icon in your taskbar system tray (near the clock) and double-click it.
Once the dashboard opens, look for the Virus & threat protection tab on the left-hand sidebar or the main menu and click it.
Step 3 – Access Manage Settings
Under the heading “Virus & threat protection settings,” you will see a blue link labeled Manage settings. Click this to enter the deeper configuration menu.
Step 4 – Add or Remove Exclusions
Scroll all the way to the bottom of this page. You will find a section titled Exclusions. Click on Add or remove exclusions. You may be prompted by User Account Control (UAC) to provide administrator permission; click Yes.
Step 5 – Select File to Exclude
Click the button marked + Add an exclusion. A dropdown menu will appear offering File, Folder, File type, or Process. Select File, browse to the location of the file you want to keep safe, and click Open. The path will now appear in your list of exclusions.
Advanced Methods to Exclude Files
For IT administrators or those who prefer using a keyboard over a mouse, Windows provides more powerful ways to manage these settings.
Using PowerShell Commands
PowerShell allows you to script exclusions, which is great if you are setting up multiple machines. To add an exclusion, right-click the Start button, select Terminal (Admin) or PowerShell (Admin), and type:
Add-MpPreference -ExclusionPath "C:\Your\Path\Here"
This takes effect immediately without needing to navigate through the GUI.
Using Group Policy (Pro Users)
If you are on Windows 10/11 Pro or Enterprise, you can use the Group Policy Editor (gpedit.msc). Navigate to Computer Configuration > Administrative Templates > Windows Components > Microsoft Defender Antivirus > Exclusions. This is the best way to ensure exclusions remain permanent and cannot be easily changed by other users.
How to Remove or Edit Exclusions
It is a good habit to audit your exclusion list every few months. If you no longer use a specific tool, remove its exclusion. Navigate back to the Add or remove exclusions page in Windows Security, click the arrow next to the entry you wish to delete, and click Remove. This restores full protection to that path instantly.
Troubleshooting Common Issues
Windows Security Exclude Folder Not Working
Sometimes, even after adding a folder to the exclusion list, Windows might still flag files. This usually happens because of environment variables. For example, if you exclude %AppData%\Tool, but the system recognizes it as C:\Users\Name\AppData\Roaming\Tool, there might be a conflict. Always try to use the absolute, full path (starting with C:) to ensure the rule sticks. Additionally, ensure that Controlled Folder Access isn’t the feature blocking the file, as it maintains its own separate whitelist.
Stop Windows Defender from Deleting Recovered Files
One of the most heart-wrenching moments in data recovery is seeing your lost files reappear, only for Windows Security to delete them again immediately because it perceives the “raw” recovered data as a threat. When data is recovered from a corrupted drive, it often lacks the proper metadata, causing it to look like “garbage data” or malware to a scanner.
To stop windows defender from deleting recovered files, you should create a dedicated “Recovery” folder on your desktop and add that entire folder to the exclusion list before you start the recovery process. This creates a safe zone where your data can be landed and inspected manually without the antivirus intervening.
Using PandaOffice Drecov Data Recovery Software
When standard file management fails and you find yourself missing critical data—perhaps due to an accidental deletion or a security software “cleanup”—you need a professional-grade tool. PandaOffice Drecov data recovery software is designed to handle complex retrieval tasks while being user-friendly enough for beginners.
⚠ Warning: Install it to a drive other than the one you are trying to recover data from to avoid overwriting your lost files. Launch the application with Administrator privileges.
Unlike basic undelete tools, PandaOffice Drecov uses deep-sector scanning technology to find fragments of files that the operating system no longer tracks. Here is how to use it effectively:
Step 1: Preparation and Exclusion
Create a folder named C:\DrecovRecovery. Follow the steps mentioned earlier in this article to add this folder to your Windows Security exclusions. This ensures that as PandaOffice Drecov data recovery software extracts files, they aren’t stripped away by real-time protection.
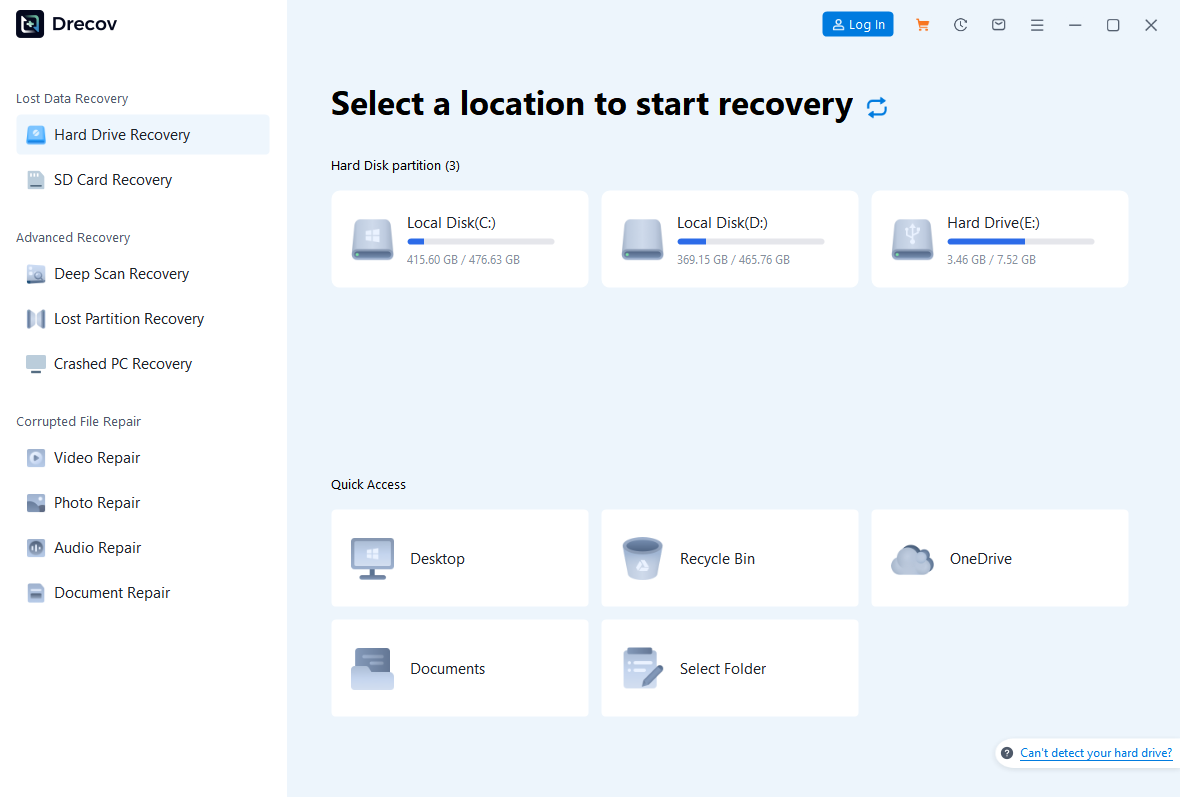
Step 2: Select the Target Location
Upon launching, you will see a list of all connected drives (HDD, SSD, USB, etc.). Select the partition where your files were last seen. Click the Scan button to begin the analysis.
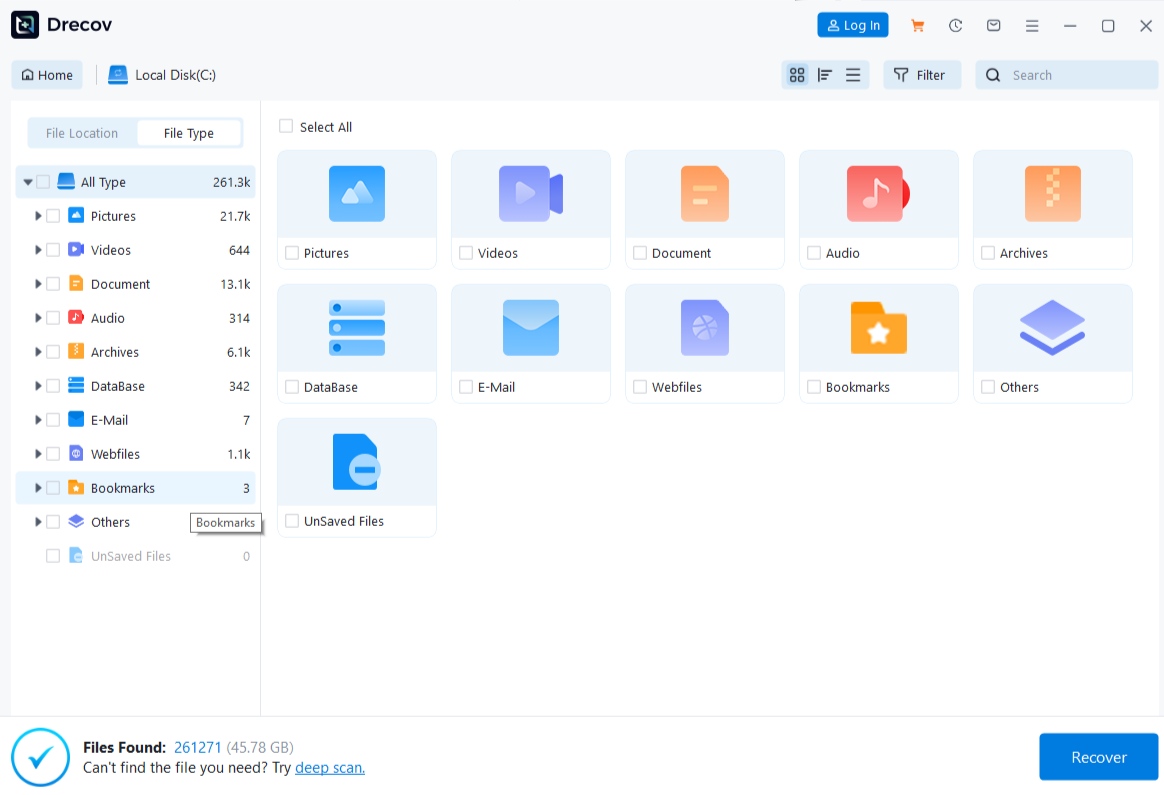
Step 3: Preview and Filter
One of the best features of PandaOffice Drecov data recovery software is the real-time preview. As the scan progresses, you can click on images or documents to see if they are intact. Use the filter sidebar to search by file extension (e.g., .jpg, .docx, .pdf) to save time.
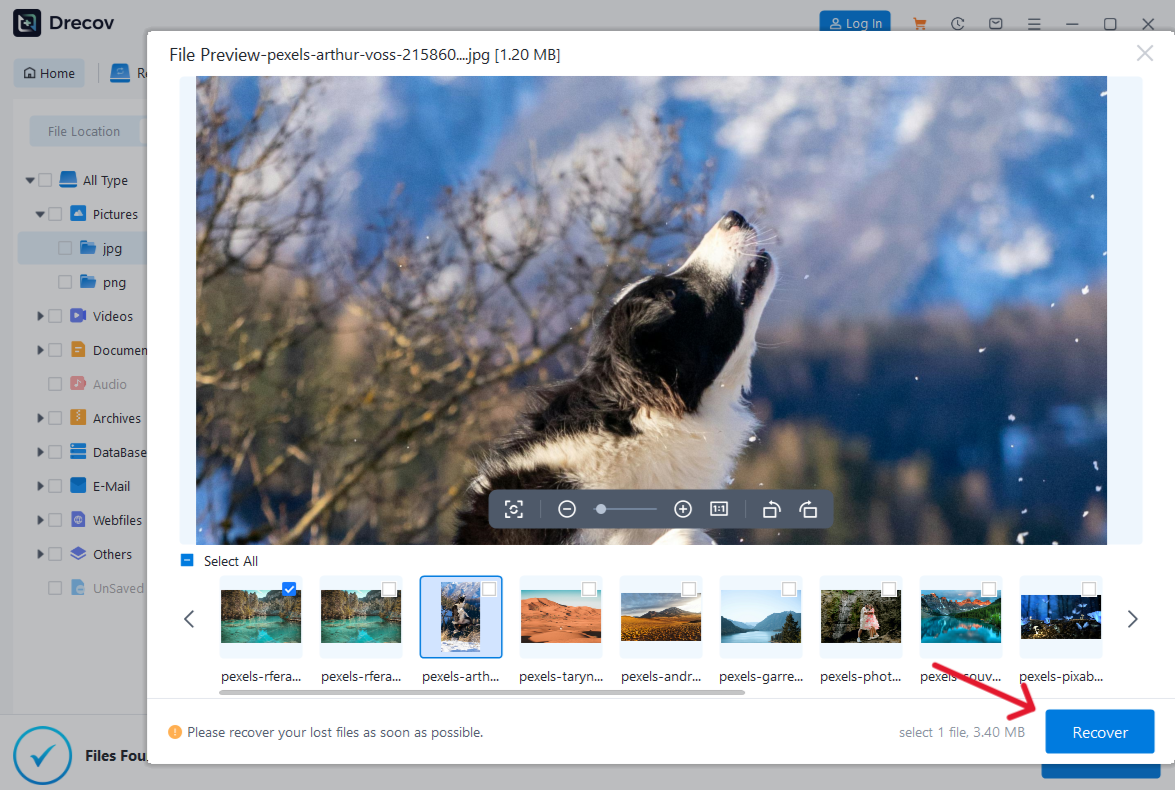
Step 4: Execute the Recovery
Check the boxes next to the files you wish to save. Click the Recover button.
Warning: Always save your recovered files to a different physical drive or the excluded folder you created in Step 1. Saving back to the same drive significantly increases the risk of permanent data corruption.
Mastering File Recovery Contexts
Data recovery isn’t just about clicking a button; it’s about understanding the environment. Once you have successfully recovered your files using the methods above, you might find yourself needing to manage specific file types or large batches of data.
For instance, if you’ve recovered a large number of text documents, you should learn how to use txt files in Windows and recover lost data to ensure your formatting remains intact. If you are dealing with a massive data loss event on the latest OS, knowing how to find deleted files on Windows 10/11 instantly can save you hours of panic. Finally, once your files are back, you’ll likely need to move or organize them; mastering how to select multiple files on Windows and recover lost data efficiently is the final step in a successful recovery workflow.
Best Practices to Maintain Security
While we have focused heavily on how to exclude files from windows security, the goal is always a healthy system. Exclusions should be the exception, not the rule.
- Update Regularly: Ensure Windows is updated so the antivirus has the latest definitions, which reduces false positives.
- Layered Defense: Use a standard user account for daily tasks and keep the Administrator account only for when you need to change security settings.
- Backup Strategy: No amount of exclusions or recovery software replaces a solid backup. Follow the 3-2-1 rule: 3 copies of your data, on 2 different media, with 1 copy off-site.
How to Exclude Files from Windows Security FAQs
1. Is it safe to exclude files from Windows Security?
It is safe only if you are certain the file is clean. Always scan the file with an online multi-scanner tool before adding it to your exclusion list.
2. Why does Windows Security keep deleting my files even after exclusion?
This often happens if the “Controlled Folder Access” feature is enabled or if the exclusion path was entered incorrectly. Check for typos or environment variable errors.
3. Can I exclude an entire folder?
Yes, but be aware that any malware that enters that folder in the future will be ignored by the scanner. This is a significant security risk.
4. Do exclusions affect real-time protection?
Absolutely. Exclusions tell the real-time protection engine to skip those specific paths during its active monitoring cycle.
5. How often should I review exclusions?
Ideally, you should audit your exclusion list every 3 to 6 months. Remove any entries for software you no longer use to minimize your attack surface.
6. Will PandaOffice Drecov work if my drive is formatted?
Yes, PandaOffice Drecov data recovery software can often recover data from formatted or RAW partitions, provided the data has not been overwritten by new files.
Conclusion
Mastering the art of how to exclude files from windows security allows you to take full control of your computing environment. Whether you are a developer looking for more speed, a gamer trying to run a custom mod, or a victim of data loss trying to stop windows defender from deleting recovered files, the steps outlined here provide a safe roadmap. By using professional tools like PandaOffice Drecov data recovery software and understanding the technical “why” behind security scans, you can ensure your data remains both accessible and protected.