In the modern digital landscape, navigating the fine line between system security and software functionality can be a daunting task. Many users often find themselves in a predicament where Windows Security—the built-in sentinel of the Windows operating system—quarantines or deletes essential files. Whether you are a developer testing custom scripts, a gamer applying a localized patch, or a professional trying to access niche tools, knowing how to let crack file through windows security safely is a vital skill.
However, modifying security settings is only half the battle. Frequently, these aggressive security scans lead to the accidental loss of important data. Therefore, this guide not only covers the nuances of security exclusions but also provides a deep dive into professional data recovery techniques using advanced tools like PandaOffice Drecov. By the end of this article, you will have a 360-degree understanding of how to manage your digital environment without compromising your precious files.
Understanding the Architecture of Windows Security
Before we dive into the mechanics of how to let crack file through windows security, we must first understand what we are dealing with. Windows Security, formerly known as Windows Defender, is a robust, multi-layered defense system. It utilizes heuristic analysis, cloud-delivered protection, and signature-based detection to identify threats.
The Role of Real-Time Protection
The real-time protection engine is the heart of Windows Security. It monitors every file interaction on your system. When you download a file, the engine checks its digital signature and compares its code against a massive database of known threats. If a file—such as a “crack” or a keygen—lacks a valid signature or behaves in a way that resembles a trojan, Windows Security will instantly neutralize it.
Why Do “Crack” Files Get Flagged?
It is important to acknowledge that “crack” files are designed to modify the behavior of other software. From the perspective of an antivirus, this “modification” is indistinguishable from malicious injection. Consequently, the system triggers a false positive. While the intent of the user is benign, the action performed by the file is technically a security violation. Understanding this helps you realize that learning how to let crack file through windows security is essentially about manually vouching for a file’s integrity.
How to Let Crack File Through Windows Security
Managing exclusions requires a balance of precision and caution. Below is the step-by-step breakdown of how to allow specific files to bypass the security layers of Windows 10 and Windows 11.
Method 1: Adding a Specific File Exclusion
This is the most recommended method because it limits the security “blind spot” to a single file rather than a whole folder.
- Step 1: Click the Start button and type Windows Security, then press Enter.
- Step 2: Navigate to the Virus & threat protection tab on the left-hand sidebar.
- Step 3: Under the Virus & threat protection settings section, click on Manage settings.
- Step 4: Scroll down to the bottom to find Exclusions and click Add or remove exclusions.
- Step 5: Click the + Add an exclusion button and select File.
- Step 6: A file explorer window will appear. Browse to the specific “crack” or blocked file, select it, and click Open.
Method 2: How to Make Windows Security Ignore a File via Folder Exclusion
If your software consists of multiple components that keep getting flagged, you might need to know how to make windows security ignore a file by excluding its parent directory. This is more efficient for complex installations but requires higher trust in the source.
- Step 1: Create a dedicated folder (e.g.,
C:\TrustedTools) where you plan to store your specific files. - Step 2: Open Windows Security and go to Virus & threat protection > Manage settings.
- Step 3: Click Add or remove exclusions under the Exclusions header.
- Step 4: Choose Add an exclusion and this time select Folder.
- Step 5: Select your dedicated folder. Now, any file moved into this folder will be ignored by the real-time scanner.
Warning: Never exclude your “Downloads” or “Desktop” folders entirely. Doing so would allow actual malware to hide in plain sight without being detected.
The Hidden Danger: When Security Deletes Your Data
A common side effect of learning how to let crack file through windows security is discovering that the file has already been deleted or corrupted by the system before you could exclude it. When Windows Security detects a “high-risk” threat, it doesn’t always ask for permission; it often moves the file to a quarantine zone or wipes it from the disk to protect the kernel.
If you find that your important files—whether they are work documents, project assets, or specialized tools—have vanished due to an overzealous antivirus, you need a robust recovery strategy.
Recovering Lost Data with PandaOffice Drecov Data Recovery Software
When a file is “deleted” by Windows, the data often remains on the physical sectors of the hard drive or SSD for a short period. PandaOffice Drecov data recovery software is specifically engineered to scan these deep layers of storage to reconstruct and retrieve files that the operating system no longer sees.
Why Choose PandaOffice Drecov?
Unlike basic undelete tools, PandaOffice Drecov utilizes advanced scanning algorithms that can handle various file systems, including NTFS, FAT32, and exFAT. It is particularly effective after a Windows Security intervention because it can identify file fragments even if the file header was modified during the quarantine process.
⚠ Warning: Install it on a drive different from the one where your data was lost to prevent overwriting.
Step-by-Step Recovery Process with PandaOffice Drecov
Follow these steps to retrieve files that were lost during your attempt to manage security settings:
- Step 1: Selecting the Target Location. Launch the program. You will see a dashboard displaying all connected drives. Select the drive (usually C: or an external USB) where the flagged file was originally located.
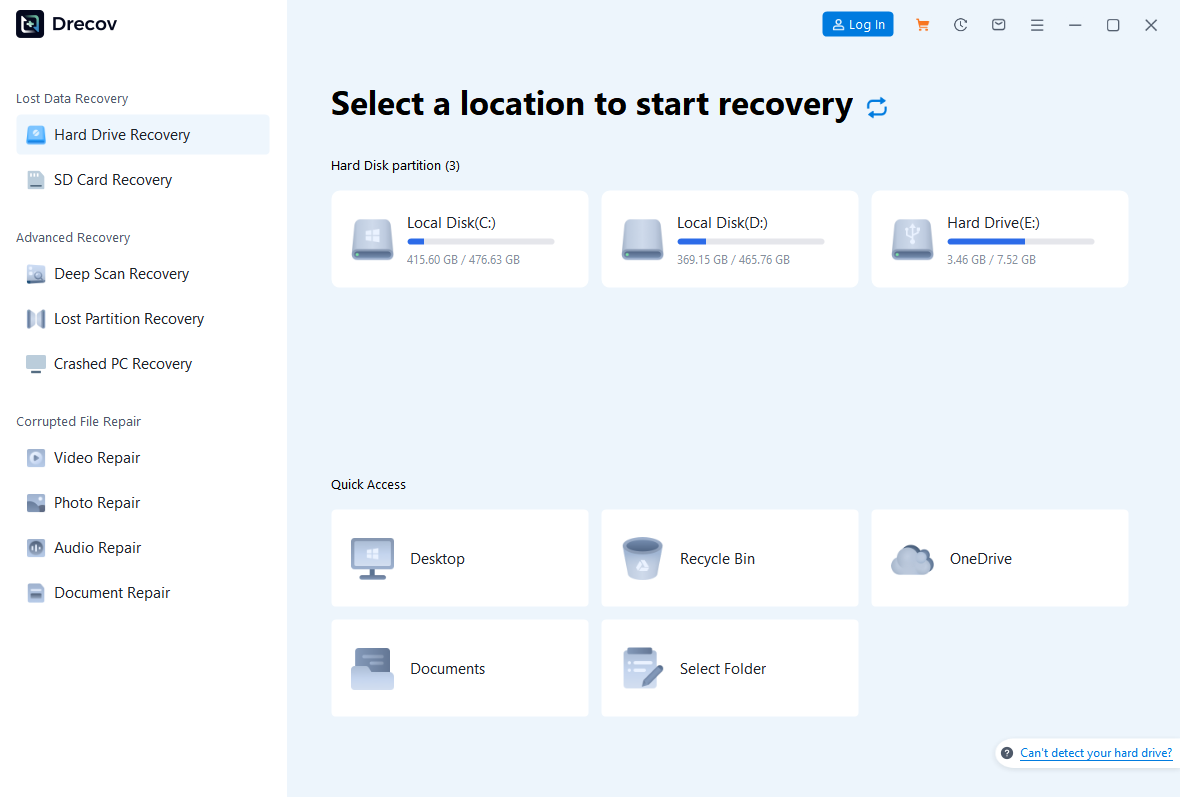
- Step 2: Deep Scanning for Signatures. Click the Scan button. PandaOffice Drecov data recovery software will perform a Quick Scan followed by a Deep Scan. The Deep Scan is crucial here, as it looks for raw file signatures which is helpful if Windows Security attempted to shred the file.
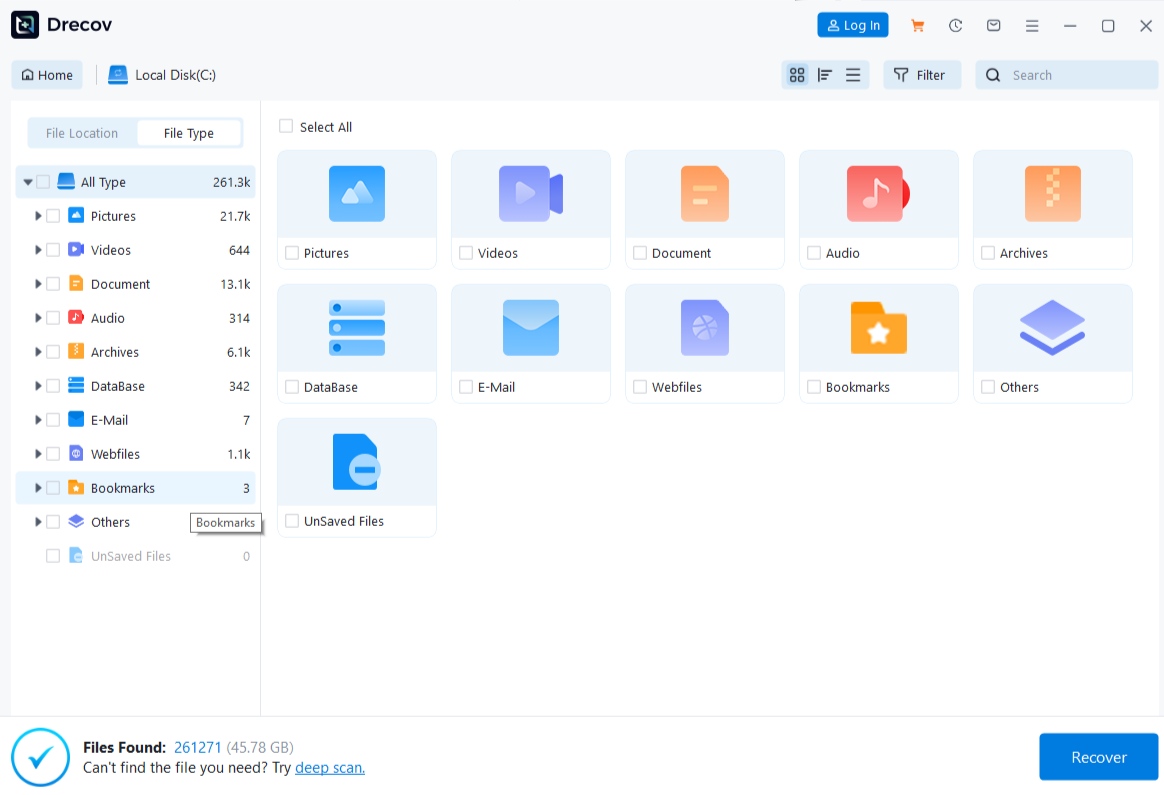
- Step 3: Filtering the Results. Once the scan is complete, use the sidebar to filter by file type (e.g., .exe, .dll, .zip). This makes it much easier to find the specific file you were trying to “let through” the security system.
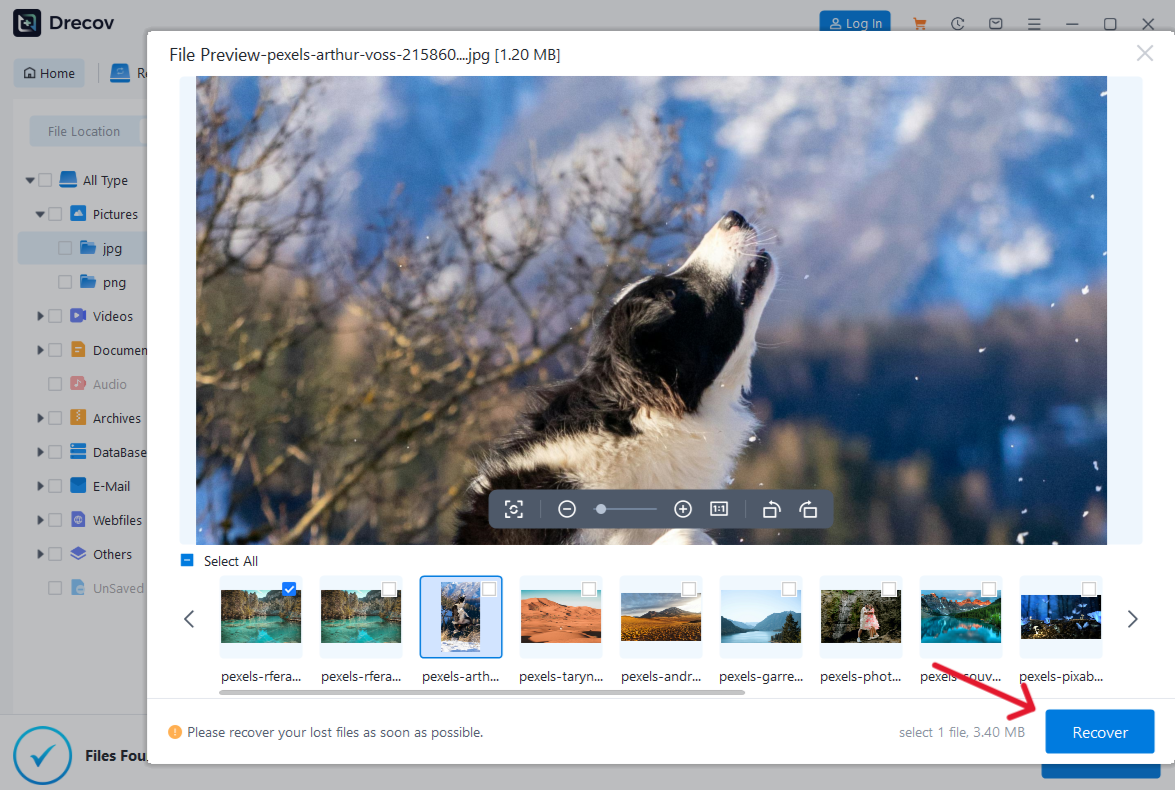
- Step 4: Preview and Validation. One of the best features of PandaOffice Drecov is the preview window. Click on a file to see its properties. If it’s a document or image, you can see the content. For application files, check the file size to ensure it matches the original.
- Step 5: Secure Recovery. Select the files you wish to restore and click Recover. Choose a destination on a different drive (like an external HDD) to save the recovered data.
Key Operation Point: If you are recovering a file that was previously flagged as a threat, make sure to disable real-time protection temporarily during the recovery process, or it might get deleted again the moment it hits your drive!
After successfully recovering your files or configuring your security settings, you may find these expert guides helpful for further optimizing your Windows experience:
- How to Use Recuva to Recover Deleted Files: 2026 Expert Guide – A deep dive into alternative recovery methods.
- How to Install Drivers for USB 3.0 to HDMI Adapter on Windows 11 – Resolve hardware connectivity issues that might interfere with data transfer.
- How to Download Video from Browser Firefox: 2026 Guide – Learn safe ways to acquire media without triggering security alerts.
Advanced Technical Tips for Power Users
If the standard GUI methods for how to let crack file through windows security are failing, or if the “Add an exclusion” button is greyed out, you may be dealing with administrative restrictions or a corrupted security registry.
Using PowerShell for Exclusions
PowerShell offers a direct line to the Windows Defender API. This is often more reliable than the Settings app.
- Right-click the Start button and select Terminal (Admin) or PowerShell (Admin).
- To add an exclusion, type the following command and press Enter:
Add-MpPreference -ExclusionPath "C:\Path\To\Your\File.exe" - To verify the list of excluded paths, use:
Get-MpPreference | Select-Object ExclusionPath
Registry Editor Modification
In rare cases, you may need to manually verify if exclusions are being registered in the Windows Registry. The path for these settings is:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Defender\Exclusions\Path
Note: Accessing this key requires SYSTEM level permissions, and manual editing is generally discouraged unless you are an IT professional.
For more official documentation on how Windows handles these threats, you can visit the Microsoft Security Documentation.
Data Recovery Scenarios: Beyond Antivirus Deletions
While this guide focuses on how to let crack file through windows security, it’s worth noting that PandaOffice Drecov is a versatile tool for many other data loss scenarios. Data recovery is a broad field, and mastering it requires understanding different failure modes.
1. USB and External Drive Recovery
External drives are prone to file system corruption if unplugged without “safely removing” them. If your “crack” file was on a USB stick and the stick now shows as “RAW” or “Unformatted,” PandaOffice Drecov can bypass the file system error and read the data directly from the NAND flash cells.
2. Recovery After a System Crash
Sometimes, trying to run unverified software can cause a Blue Screen of Death (BSOD). If a crash occurs while a file is being written, it can lead to “orphan files.” PandaOffice Drecov data recovery software excels at reassembling these orphans into functional files.
Maximizing Your SEO and System Health
From an SEO and technical standpoint, maintaining a healthy system is about more than just avoiding viruses; it’s about data integrity. When you search for terms like how to make windows security ignore a file, you are looking for autonomy over your machine. However, autonomy comes with the responsibility of maintenance.
Best Practices for System Maintenance
- Update Regularly: Even if you use exclusions, keep Windows Security updated so it can catch actual threats that you haven’t excluded.
- Cloud Backups: Use services like OneDrive or Google Drive for your documents, so that if a local exclusion goes wrong and malware enters, your primary work is safe.
- Audit Your Exclusions: Every six months, go back to the Windows Security settings and remove exclusions for software you no longer use.
Comparative Table: Manual Exclusion vs. Data Recovery
| Feature | Manual Exclusion (Settings) | PandaOffice Drecov Recovery |
| Primary Goal | Prevent future deletion | Retrieve already deleted files |
| Complexity | Low (Point and click) | Medium (Scan and filter) |
| Risk Level | Increases vulnerability | No risk to system security |
| Prerequisite | File must still exist | File can be missing or deleted |
| Success Rate | 100% (Prevents scan) | High (Depends on disk usage) |
Frequently Asked Questions
Can I exclude a file by its extension?
Yes. In the Add an exclusion menu, you can select File type and enter an extension like .exe. This will make Windows Security ignore every executable on your computer. Warning: This is extremely dangerous and is not recommended for general users.
Will adding an exclusion slow down my computer?
Actually, it might speed it up slightly. Since the antivirus is no longer scanning those specific files, CPU usage during the execution of those programs will decrease. However, the performance gain is usually negligible unless you are excluding a very large database or a folder with thousands of small files.
What should I do if PandaOffice Drecov cannot find my file?
If a Deep Scan does not show your file, it may have been overwritten by new data. Stop using the drive immediately. Check if the file was moved to the Protection History in Windows Security instead of being deleted. You can often “Restore” files directly from the Protection History if they haven’t been purged yet.
Is there a limit to how many exclusions I can add?
Technically, there is no hard limit, but having hundreds of exclusions can make your system vulnerable and difficult to manage. Stick to excluding only what is strictly necessary for your workflow.
By following this guide, you now possess the knowledge to handle the most common conflicts between user intent and system security. Whether you are adjusting settings or recovering lost assets with PandaOffice Drecov, you are in control of your digital environment.
Conclusion
Mastering how to let crack file through windows security is a fundamental skill for any power user who wants to use their PC without constant interference. By following the steps to add file and folder exclusions, you can ensure your specialized tools remain untouched.
However, accidents happen. Files get deleted, drives get corrupted, and security software can sometimes be a bit too aggressive. In those moments, having a professional tool like PandaOffice Drecov data recovery software in your arsenal is the ultimate safety net. It allows you to experiment and customize your system with the peace of mind that your data can always be brought back from the brink.